Cyber Security is the process of preventing malicious attacks on internet-connected equipment such as PCs, servers, cell phones, electronic networks, and information systems. Cybersecurity can be broken down into two parts: cyber and security. Cyber refers to the field of technology that covers systems, networks, software, and data. Security is concerned with safeguarding systems, networks, applications, and data.

Definitions of Cybersecurity
Cybersecurity is a set of guidelines and procedures to safeguard our data and computing resources from any kind of dangers. It is the practice of preventing online assaults, unauthorized access, damage, and theft of computer systems, networks, programs, and data.

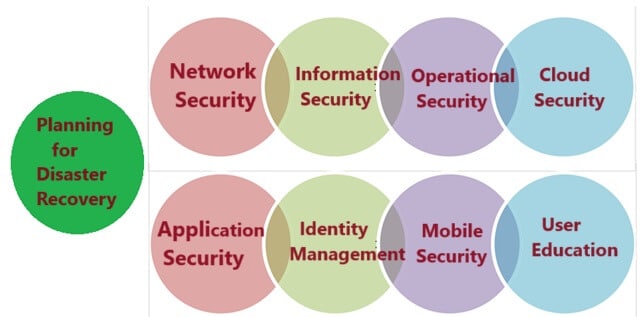
Sub-Domains of Cyber Security
An organization’s assets are the result of combining various systems. Coordination of actions across these systems is necessary due to the strong cybersecurity posture of these systems. As a result, we can group cybersecurity into the subsequent sub-domains:
-
Network Security:
The implementation of hardware and software to protect a computer network from misuse, illegal access, intrusions, and attacks is known as network security. An organization’s assets are better protected from both internal and external threats with the use of this security.
-
Application Security:
It safeguards devices and software against unauthorized access. To keep the apps safe from intrusions, it is possible to achieve this protection by updating them frequently. Before a program or device is implemented, successful security must start in the design phase, which includes authoring source code, validation, threat modeling, etc.
-
Information Security:
In order to protect the integrity and privacy of data while it is being stored and transferred, a robust data storage system must be put in place. This is known as information or data security.
-
Identity Management:
It is the process of figuring out how much access each person has inside an organization.
-
Operational Security:
It includes evaluating data and making choices about how to handle and safeguard data assets.
-
Mobile Security:
It involves safeguarding personal and corporate data from several dangerous threats that may be encountered when using portable technology, like laptops, tablets, and cell phones. These risks include the virus, device loss or theft, and unauthorized access.
-
Cloud Security:
It is the process of safeguarding data kept in an organization’s cloud infrastructures or digital environments. It makes use of a number of cloud service providers, namely Google, AWS, Azure, and others, to provide security from various kinds of threats.
-
Planning for Disaster Recovery and Business Continuity:
This includes procedures, notifications, and strategies for what to do when malicious activity results in an organization’s operations or data being lost. According to its policies, activities must be resumed following a disaster at the same level of capability as before the incident.
-
User Education:
It focuses on how an organization reacts in the event that harmful conduct results in the loss of operations or data. It includes processes, monitoring, alarms, and plans. According to its policies, operations must be restored to their pre-disaster level as soon as possible.
Importance of Cybersecurity
Today we live in a virtual generation wherein all components of our lives rely upon the network, PC, different digital devices, and software program applications. Internet-connected devices are an essential part of all key infrastructure, including the banking system, healthcare system, monetary systems, governments, and manufacturing businesses.
Some of their data, including financial, personal, and intellectual property, may be at risk of unwanted access or exposure that could have negative impacts. With this information, threat actors and invaders can target them for vandalism, extortion, political or social gain, or plain cash benefit.
Cyber-attacks are a global concern that hack the system, and additional security attacks could harm the stability of the world economy. So, to shield confidential data from security breaches, having a strong cybersecurity plan is necessary.
In addition, as the number of cyberattacks rises, businesses and institutions—particularly those handling data related to health, finances, or national security—need to implement robust cybersecurity procedures and safeguards to safeguard their confidential and private data.
Goals for Cyber Security
Cybersecurity’s main objective is data protection. To safeguard data from cyberattacks, the security community offers a triangle including three interconnected concepts. Concept is called as the “CIA trio”. An organization’s information security infrastructure policies are intended to be guided by the CIA model. A violation of one or more of these criteria is detected when security breaches occur.

The CIA model consists of three parts: confidentiality, integrity, and availability. It is, in fact, a security model that aids in the conceptualization of many aspects of IT security. Let’s talk about each section in more detail.
1. Confidentiality
Privacy that keeps information from being accessed by unauthorized parties is the same as confidentiality. It entails making sure the data is accessible to those who are authorized to use it and preventing unauthorized access. It keeps important information from getting into the wrong hands. Encrypting data is a great way to guarantee confidentiality.
2. Integrity
In accordance with this approach, data is guaranteed to be genuine, accurate, and protected against unintentional user alteration or illegal modification by threat actors. The sensitive data should be protected from corruption or loss, and steps should be taken to quickly recover in the event that any modifications are made. Furthermore, it suggests verifying the authenticity of the information source.
3. Availability
This principle ensures that information is constantly accessible to and helpful to those who are authorized to access it. It makes sure that cyberattacks or system errors don’t prevent these accesses.
Different Types of Cyber Security Threats
In the field of cybersecurity, a threat is any harmful activity carried out by a person or organization with the intent to steal or corrupt data, get access to a network, or interfere with everyday digital life. The following threats are currently identified by the cyber community:

1. Malware as Cybersecurity Threat
Malware, short for malicious software, is the most popular tool used in cyberattacks. The hacker or cybercriminal uses it to interfere with or harm the system of an authorized user. The key categories of malware that the hacker produced are as follows:
- Virus: A harmful piece of code that passes from one device to another is called a virus. It can destroy devices, steal information, contaminate data, and spread throughout a computer system.
- Trojans: It’s a kind of virus or code that poses as trustworthy files or software in order to trick us into downloading and using it. Its main objective is to damage or steal data from our device or carry out other malicious activities on our network.
- Spyware: It’s software that secretly logs data about what users do on their computers. For instance, credit card information might be captured by spyware, which would then be utilized by cybercriminals to make unapproved purchases, withdraw money, etc.
- Worms: It is a software program that replicates itself automatically between devices in the absence of human intervention. They can steal or corrupt the data without attaching themselves to any program.
- Ransomware: Software known as “ransomware” encrypts user files and data on a device, making them impossible to access or possibly destroying them. Malicious actors then demand payment in exchange for the decryption key.
- Botnets: Botnets are groups of devices infected with malware that are connected to the internet and can be controlled by hackers. Without the user’s approval, it gives hackers access to credentials leaks, unauthorized access, and data theft.
- Adware: On our device, it is an advertising software that spreads malware and shows ads. Without the user’s approval, unwanted software installed itself. By displaying advertisements in their browsers, this program’s primary goal is to make money for its creator.
2. Phishing as Cybersecurity Threat
Phishing is a kind of cybercrime where the sender poses as someone from a reliable source, such as PayPal, eBay, financial institutions, or even friends and colleagues. They reach out to a target or targets by phone, text message, or email and offer a link in an attempt to attract them to click it.
By clicking on this link, scammers direct the users to fake websites where they will ask the customers to provide sensitive information such as usernames, passwords, social security numbers, banking and credit card information, and personal information. Additionally, by clicking the link, malware that enables remote device control will be installed on the target devices.
3. Man-in-the-middle (MITM) Attack – Cybersecurity Threat
An example of a cyber danger is a man-in-the-middle attack, which is an eavesdropping attack where a cybercriminal eavesdrops on a conversation or data transfer between two people. Once the cybercriminal inserts themselves into a two-way conversation, they can obtain sensitive information and respond with varied responses while appearing to be trustworthy participants.
This kind of attack’s primary goal is to obtain our company’s or our customers’ data. For instance, on an open Wi-Fi network, a cybercriminal could collect data traveling between the target device and the network.
4. Distributed denial of service (DDoS) – Cybersecurity Threat
A cyber threat or malicious effort of this kind occurs when fraudsters use legitimate requests to the target or its surrounding infrastructure with Internet traffic, disrupting ordinary traffic on the servers, services, or networks.
The requests originate from multiple IP addresses in this case, which could render the system unworkable, overload the servers, cause them to slow down considerably, go offline temporarily, or restrict an organization’s ability to perform essential tasks.
5. Brute Force – Cybersecurity Threat
A brute force attack is a type of cryptographic hacking where all potential combinations are attempted until the right information is found through trial and error. Cybercriminals typically use this technique to gain sensitive data, including targeted passwords, login credentials, encryption keys, and Personal Identification Numbers (PINS).
6. SQL Injection (SQLI) – Cybersecurity Threat
A frequent attack known as SQL injection takes place when hackers utilize malicious SQL scripts to manipulate backend databases and get access to private data. The malicious actor can see, alter, or remove confidential customer information, user lists, and sensitive company data kept in the SQL database when the attack is successful.
7. Domain Name System (DNS) Attack – Cybersecurity Threat
Cybercriminals can utilize DNS hijacking, a technique that reroutes users to malicious websites, and take advantage of vulnerabilities in the system to steal data from affected computers. Due to the DNS system’s importance to the internet’s infrastructure, there is a serious cybersecurity risk.
Latest Cyber Security Threats
As new attack vectors appear and cybercriminals become more skilled, the nature of cyber threats is always changing. The following are some of the most recent cyber threats that people and businesses should be aware of:
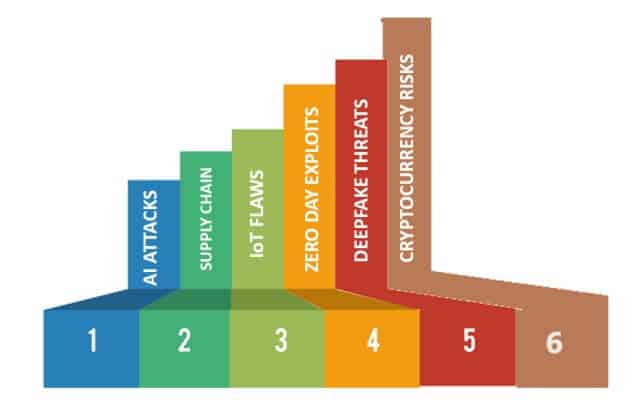
- AI-Driven Attacks: Cybercriminals utilize artificial intelligence (AI) to automate and improve their attacks, making them more complex and challenging to identify.
- Supply Chain Attacks: Cybercriminals are progressively focusing on the supply chain, targeting software upgrades, third-party vendors, and service providers to obtain entry to their desired targets.
- IoT Security Flaws: Cybercriminals can launch attacks on Internet of Things (IoT) devices due to their frequent lack of security, which makes them vulnerable to attacks like DDoS and botnet attacks.
- Zero-day Exploits: Zero-day vulnerabilities are defects in software that the vendor is unaware of. These vulnerabilities are a serious issue because cybercriminals can quickly take advantage of them before one can fix it.
- Deepfake Threats: Any one can use deepfake technology to create Realistic false audio and video footage. Scammers use it for fraud, blackmail, or misinformation.
- Risks Associated with Cryptocurrencies: Due to their popularity, fraudsters continue to utilize ransomware payments, fraud, and virus mining.
Both individuals and organizations need to continue taking a proactive approach to cybersecurity in order to be safe from these most recent cyber threats. This also entails updating systems and software, putting strong security measures in place, warning users about cyber threats, and being up-to-date on new threats and attack strategies.

Advantages of Cyber Security
The following are some of the benefits of cybersecurity:
- Protection from Cyber Threats: Cybersecurity protects against phishing, malware, and other dangers that could cause data breaches and financial losses.
- Data Privacy: It protects sensitive information by ensuring data privacy and confidentiality.
- Continuity of Business: Cybersecurity protocols prevent downtime by preserving operations and customer trust.
- Reputation Preservation: A robust cybersecurity posture always safeguards an organization’s reputation.
- Legal Compliance: It assists businesses in following rules and staying out of trouble with the law.
- National Security: Protecting sensitive government data and essential infrastructure requires cybersecurity.
Disadvantages of Cyber Security
The following are some of the drawbacks of cybersecurity:
- Resource-intensive: Especially for small enterprises and individuals, implementing and maintaining efficient cybersecurity measures can be expensive.
- Changing Threat Environment: Due to the continuous evolution of cyber threats, individuals and organizations must stay aware of emerging attack methods and security flaws.
- User Opposition: Users who find strict cybersecurity regulations burdensome or detrimental to their productivity may oppose them.
- Over-dependence on Technology: Putting too much reliance on technology in security measures can lead to vulnerabilities. It is because it just takes a single technological fault or compromise to cause a breach.
- Complexity: Managing and implementing cybersecurity solutions can be challenging, particularly for non-technical individuals. This might result in oversights or incorrect configurations.
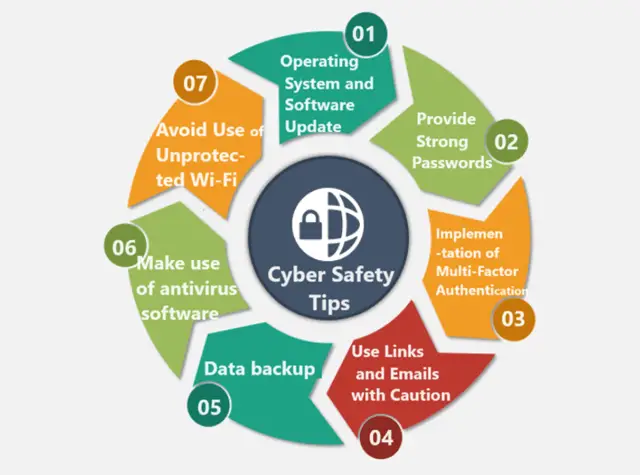
Cyber Safety Tips
Let’s examine how to safeguard ourselves in the case of a cyberattack. The most popular tip for cyber safety is as follows:
-
Update the Operating System and Software:
Getting the most recent security patches by updating OS and software is the best safety precaution.
-
Provide Strong Passwords:
It’s advisable to create long, complex passwords with a variety of letter and symbol combinations. It makes it difficult for someone to guess the passwords.
-
Implementation of Multi-Factor Authentication:
Before allowing access to an account or system, users must submit two or more forms of authentication. You can do this using Multi-Factor Authentication (MFA), a security technique. Typically, this entails the user’s knowledge (password), possessions (mobile device for code retrieval), and identity (biometric data, such as fingerprint or facial recognition). It will provide an additional degree of security against unwanted access.
-
Use Links and Emails with Caution:
Avoid opening email attachments from senders you are not familiar with. Cyber experts always caution against opening or clicking any attachments. This include unknown or from websites you are unfamiliar with, since they may contain malware.
-
Data backup:
All organizations need to routinely perform data backups to prevent the loss of sensitive information due to security breach. Backups are useful in preserving data integrity during ransomware, phishing, and SQL injection cyberattacks.
-
Make use of antivirus software:
Antivirus software can help identify and eliminate undesired threats from your device. You should update your antivirus constantly to obtain the highest level of protection.
-
Avoid Use of Unprotected Wi-Fi:
It’s advisable to avoid using insecure networks, as they can expose you to man-in-the-middle attacks.
Understanding and putting into practice strong cybersecurity measures are crucial for both individuals and organizations in digital world. Accordingly, we have tried to make sure that this article offers insights into the field of cybersecurity and a road map for safeguarding against changing cyber threats. Stay informed, stay secure.
Read Also: Network Security Key on Computer Network/ Router | How to Find Wi-Fi Password VPN (Virtual Private Network) – How it Works, Best VPNs, Are VPNs Legal

Hello! I could have sworn I’ve been to this blog before but after browsing through some of the post I realized it’s new to me. Anyways, I’m definitely happy I found it and I’ll be book-marking and checking back frequently!
As I web site possessor I believe the content matter here is rattling great , appreciate it for your hard work. You should keep it up forever! Good Luck.
Very interesting subject, regards for posting. “Education a debt due from present to future generations.” by George Peabody.
hello there and thank you for your information – I’ve definitely picked up anything new from right here. I did however expertise some technical points using this web site, since I experienced to reload the website lots of times previous to I could get it to load correctly. I had been wondering if your hosting is OK? Not that I am complaining, but slow loading instances times will often affect your placement in google and could damage your quality score if advertising and marketing with Adwords. Well I am adding this RSS to my email and can look out for much more of your respective fascinating content. Make sure you update this again very soon..
I keep listening to the news update lecture about receiving free online grant applications so I have been looking around for the finest site to get one. Could you advise me please, where could i get some?
F*ckin’ tremendous issues here. I am very satisfied to see your article. Thanks so much and i am taking a look ahead to contact you. Will you please drop me a mail?
Great awesome issues here. I am very happy to peer your post. Thank you so much and i am looking ahead to contact you. Will you kindly drop me a e-mail?
Good ?V I should definitely pronounce, impressed with your web site. I had no trouble navigating through all the tabs and related information ended up being truly simple to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or anything, website theme . a tones way for your client to communicate. Nice task..
Thank you for another fantastic post. The place else may anybody get that type of information in such an ideal manner of writing? I have a presentation next week, and I am at the look for such information.
Hello there, I found your web site via Google while searching for a related topic, your site came up, it looks great. I have bookmarked it in my google bookmarks.
I think other site proprietors should take this website as an model, very clean and magnificent user friendly style and design, let alone the content. You are an expert in this topic!
Hey there! Do you use Twitter? I’d like to follow you if that would be ok. I’m absolutely enjoying your blog and look forward to new updates.
I¦ve been exploring for a little for any high-quality articles or blog posts on this kind of space . Exploring in Yahoo I at last stumbled upon this web site. Reading this info So i am satisfied to exhibit that I’ve a very good uncanny feeling I discovered just what I needed. I so much certainly will make certain to do not omit this website and give it a look regularly.
heating and air maintenance [url=https://otvetnow.ru]https://otvetnow.ru[/url] home loans first time buyers zero down
It’s actually a nice and useful piece of info. I am glad that you just shared this helpful info with us. Please keep us informed like this. Thank you for sharing.
You should take part in a contest for one of the best blogs on the web. I will recommend this site!
I have mastered some new issues from your web page about computer systems. Another thing I’ve always considered is that computer systems have become an item that each household must have for many reasons. They supply you with convenient ways to organize the home, pay bills, shop, study, focus on music and perhaps watch television shows. An innovative strategy to complete these tasks has been a laptop. These pc’s are mobile, small, robust and convenient.
This is very attention-grabbing, You’re an excessively professional blogger. I have joined your rss feed and look forward to in the hunt for more of your magnificent post. Also, I’ve shared your website in my social networks!
This is really interesting, You’re a very skilled blogger. I’ve joined your rss feed and look forward to seeking more of your fantastic post. Also, I’ve shared your web site in my social networks!