Zigbee technology provides a stable, high efficient networking using low data transfer rates when the information and communication of the devices are less. While discussing about Zigbee in our previous post, we learnt about Zigbee technology, its associated network topologies, applications, advantages and disadvantages. Moving ahead from where we left, this post will discuss Zigbee Architecture (Zigbee Stack), its layers such as Physical Layer, MAC Layer, Network layer, Application Layer and its functions.
What is Zigbee Architecture (Zigbee Stack)
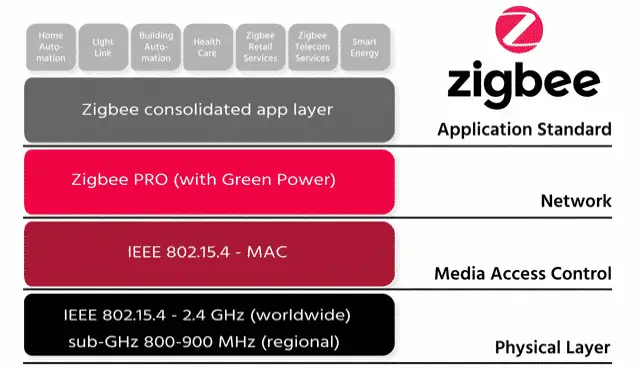
Zigbee architecture is also called Zigbee stack. It consists of two layers as the foundation on which Zigbee is built. They are:
- Foundation Layers
- Application and Interface Section
Fig. 1 – Zigbee Architecture (Zigbee Stack)
Foundation Layers in Zigbee Architecture
This Layer is defined by IEEE 802.15.4 standard. Both Physical layer and Medium Access Control (MAC) layers act as foundation layers for Zigbee Architecture.
Physical Layer in Zigbee Architecture
The physical and electrical characteristics are defined by the Physical Layer. This layer is responsible for data transmission and reception. Mapping bits of information and permits them to travel through the air by modulation and spreading techniques which is the basic task of physical layer.
Function of Physical Layer in Zigbee Architecture
Physical Layer is responsible for the following functions:
- Activation and deactivation of transmission and reception.
- Channel selection and its assessment.
- Sending and receiving of packets.
- Energy detection within the channel.
Fig. 2 – Zigbee Architecture (Zigbee Stack) Functions
Medium Access Control (MAC) Layer in Zigbee Architecture
This layer provides interface between the physical and network layers. It defines how multiple 802.15.4 radios operating in the same area will share the airwaves. Data handling and data management are the two main functions of the MAC layer.
Data handling includes functions such as “Data Request†and “Data Confirmâ€. The MAC layer adds destination address and transmits options for the outgoing data frames.
When the Zigbee network layer calls the “data request†function, the data gets formatted into relevant MAC header and frame length is added which is the physical header. The data frame is ready to be transmitted.
The purpose of “Data Confirm†function is to communicate the status of the transmitted data. It sends a fail status when the transmission frames exceeds or when there is no response to transmitted data.
Function of Medium Access Control (MAC) Layer in Zigbee Architecture
Medium Access Control (MAC) Layer is responsible for the following:
- Beacon generation and management.
- CSMA-CA (Carrier Sense Multiple Access with Collision Avoidance) is implemented.
- Guaranteed Time Clot management (GTS).
- Data frame validation and acknowledgement.
- Data transfer for upper layers.
Application and Interface Section in Zigbee Architecture
This section is defined by Zigbee Specifications and contains following two layers:
- Network Layer
- Application Layer
Network Layer in Zigbee Architecture
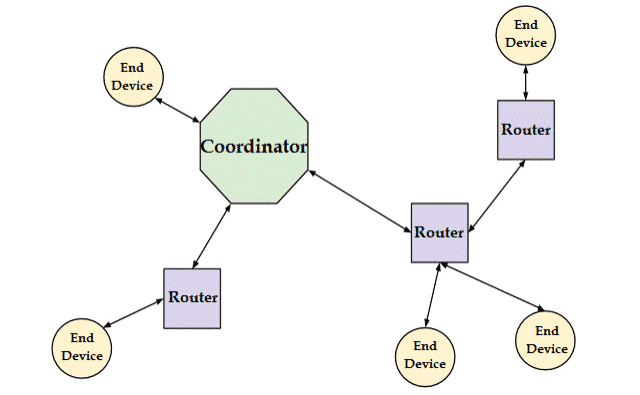
Network Layer provides interface between MAC layer and the application layer. It is responsible for routing and establishing different Zigbee network topologies namely Star, Mesh and Tree topologies.
When a coordinator attempts to establish a Zigbee network, an energy scan is initiated to find the best RF channel for its new network. When a channel has been chosen, the coordinator assigns a PAN-ID which will be applied to all the devices that join the network.
PAN-ID is a 16 bit number that is used as a network identifier. A node is allowed to communicate on a network only when it undergoes the association process. The association function is used to join a node to a parent.
Fig. 3 – Types of Network Nodes in Zigbee Architecture (Zigbee Stack)
When a node loses its parent, it is considered as an orphan device. It usually occurs when the end device is mobile and is out of range or through a failure on the parent. In such case, an orphan scan is performed by broadcasting an “orphan notification†command frame which helps the device to find its parent.
If the parent gets the notification command, it responds back to the device that it exists and the orphan can rejoin the parent. Thus the authenticity and confidentiality of a transmission is ensured by the network layer.
Function of Network Layer in Zigbee Architecture
Network Layer in Zigbee architecture is responsible for the following functions:
- Initiation of a network
- Assigning node addresses
- Configuring of new devices
- Providing secured transmission
Application Layer in Zigbee Architecture
The Application Layer in Zigbee architecture consists of sub layers namely:
- Application Support Sub Layer
- Application Framework
Fig. 4 – Automation Using Zigbee Architecture (Zigbee Stack)
Application Support Sub Layer (APS)
This layer is responsible for filtering of packets for end devices, checks for duplicity of packets which is common in a network that supports automatic retries. To maximize the chance of successful transmission, it performs automatic retries, when the acknowledgement is requested by the sender.
It is involved in maintaining binding tables. Binding is the connection between the endpoint on the node to one or more endpoints on other nodes. The address mapping associates a 64-bit MAC address with a Zigbee 16-bit network address.
Function of Application Support Sub Layer (APS)
Application Support Sub Layer (APS) is responsible for the following functions:
- Maintaining binding tables.
- Address definition, mapping and management.
- Ensuring communication between devices.
- Filtering out packets for non-registered end devices or profiles that don’t match and reassembling of the packets.
Application Framework
The Application Framework depends on the vendor who has chosen for specific applications to interact with Zigbee protocol. This represents how end points are implemented, how data requests and data confirmation is executed for that particular vendor.
Also Read: What is ZIGBEE Technology in IoT - Architecture, Network Topologies, Applications What is IoT Edge Computing – Types, Architecture, Advantages & Applications What is Smart card – How it Works, Specifications, Types and Applications