Bluetooth 5 is a short range wireless data network developed as an alternative to the messy computer accessory wires. Bluetooth allows hands free operation and also reduces desktop clutter. Bluetooth 5 can be used to connect few computers, cell phones and other devices to sync and swap files. This article entails what is Bluetooth 5 technology, its architecture (Protocol Stack), network topology used, applications, advantages and disadvantages.
What is Bluetooth 5 Technology
Bluetooth 5 is a wireless technology used for exchanging data over short distances from fixed and mobile devices. Jaap Haartsen, an electrical engineer, working for telecom vendor Ericsson invented the Bluetooth in 1994. Jim Kardach of Intel proposed the name Bluetooth in 1997, who developed a system that allowed communication of mobiles with computers.
Bluetooth has existed for almost 20 years and it has already demonstrated its robustness and dependability. With the launch of Bluetooth 5, Global wireless technology continues to advance the IoT (Internet of Things) experiences.
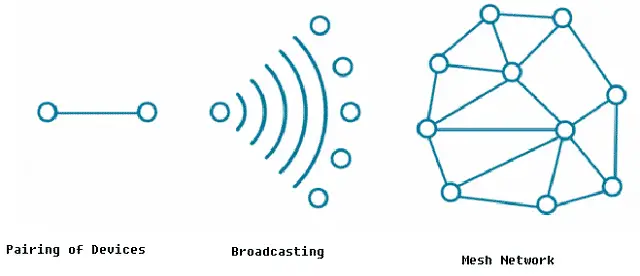
Fig. 1 – Introduction to Bluetooth 5.0
The three main features that have been introduced in Bluetooth 5 are:
- 2x the speed
- 4x the range
- 8x the advertising capacity
Fig. 2 – Bluetooth 5 Module (a) and Devices (b)
Bluetooth 5 Protocol Stack (Architecture)
Bluetooth 5 has a layer of protocol architecture which consists of core protocols, adopted protocols, cable replacement protocols, telephony control protocols, LMP, L2CAP, SDP, HCI and RFCOMM.
Fig. 3 – Bluetooth Protocol Stack
Link Manager
It is a system that manages to establish the connection between devices. The main functionality of link manager is establishment, authentication and configuration of the link. Link manager mainly consists of number of PDUs (Protocol Data Units) that are sent from one device to another device.
Host Controller Interface (HCI)
HCI provides a command interface for the controller and for the link manager, and provides an access layer for all Bluetooth devices. The most important task that must be performed is the automatic discovery of other Bluetooth devices that are within the coverage radius.
Logical Link Control and Adaptation Protocol (L2CAP)
It is used to multiplex multiple logical connections between two devices using different level protocols.
Service Discovery Protocol (SDP)
SDP allows device to discover services offered by other devices i.e., when you use a mobile with a Bluetooth headset, it uses SDP to check which Bluetooth profiles the headset can use [Hands Free Profile, Headset Profile, Advanced Audio Distribution Profile (A2DP) etc]
Radio Frequency Communications (RFCOMM)
A replacement protocol used for generating a virtual serial data stream.
Bluetooth Network Encapsulation Protocol (BNEP)
BNEP is used for transferring other protocol stack’s data using L2CAP channel.
Audio/Video Control Transport Protocol
It is used by the remote control profile to transfer AV/C commands over an L2CAP channel.
Audio/Video Distribution Transport Protocol
It is used by the advanced audio distribution profile to stream music to stereo headsets over an L2CAP channel.
Telephony Control Protocol
It is the bit-oriented protocol that defines the call control signalling for the establishment of voice and data calls between Bluetooth devices.
Adopted Protocols
This protocol is defined by other standards-making organizations and incorporated into Bluetooth’s protocol stack, allowing Bluetooth to code protocols only when necessary.
Security Concerns for Bluetooth 5 Technology
Bluetooth implements authentication, confidentiality and key generation with custom algorithms based on the SAFER+ block cipher. Bluetooth key generation is based on a Bluetooth PIN, which must be entered into both devices. This procedure can be modified if one of the devices has a fixed PIN (For example – for headsets or similar devices). There is history of security concerns for Bluetooth technology which are listed as follows:
Blue Bug
Poor implementations of Bluetooth security led to disclosure of personal data.In 2004 the first virus using Bluetooth to spread itself among mobile phones appeared on the Symbian OS. The virus was first described by Kaspersky Lab.
Lasco
A mobile malware targeted mobile phones using Symbian OS using Bluetooth enabled devices to replicate itself and spread to other devices.
Blue Borne
It allows an attacker to connect to devices or systems without authentication and can give them virtually full control over the device.
How does Bluetooth 5 Work
The Bluetooth Radio Frequency transceiver lies at the physical layer. There are about 79 Bluetooth channels and using spread spectrum technology, both voice and data transmissions over short distances occur thus creating wireless PANs.
In order to communicate, a Bluetooth device consists of an adapter which is either built into a device or it can be in the form of a card that connects to a device. Instructions are embedded into the device, which enables it to communicate with other devices.
Fig. 4 – Working Principle of Bluetooth 5
When the devices come in each other’s radio range, their link managers find each other. Link management protocol (LMP) layer performs link setup and negotiation of packet size. Segmentation and reassembling of packets is done, if necessary.
The service delivery protocol enables a Bluetooth device to join the network. Each device has a Bluetooth Global ID (a unique identification for each device) and this ID is exchanged and matched between the devices and thus a connection is set up.
Bluetooth 5 technology utilizes the concept of a mesh topology to communicate between the devices in a network. This topology uses frequency hopping in time slots i.e. the signals avoid interference with other signals by hopping to a new frequency after transmission or reception of every packet. One packet overlays five time slots.
Network Topology
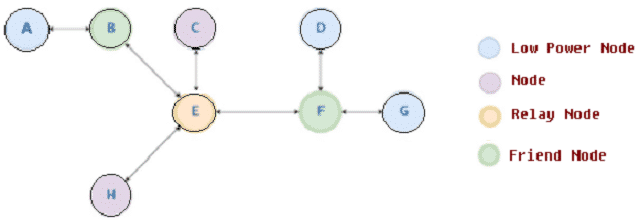
Bluetooth 5 technology utilizes a mesh topology. In a mesh network the nodes are capable of rebroadcasting the messages not intended for themselves, and helps the devices to communicate directly with each other without going through a master device ï¬rst.
Fig. 5 – Example of Bluetooth Mesh Network Topology
In the above example shown, suppose node H intends to send a message to node G, then node H sends his message with destination G to all its neighbor nodes i.e. to node E. Since E is not the destination node, it relays the message to all its neighboring nodes i.e. to B, C and F.
As B is not the destination node and the node G is not a friend node, it discards the message. Similarly C node discards the message as it is neither a destination node nor a relay node. F is a friend node of G, it accepts the message for G and waits for the request message from G. The G node requests F by sending a poll message. F receives the message from G and in response sends the confirmation message.
Applications of Bluetooth 5
The applications of Bluetooth’5 are as follows:
- Bluetooth 5 technology can be incorporated in peripherals like Wireless Keyboard, mouse, smartphones, headsets, printers.
- Used in Wireless speakers, car audio systems which helps hands free pairing with mobile devices.
- Virtual Reality and Augmented Reality systems.
- High Definition video and audio streaming applications.
- Sports and fitness tracking devices and applications.
- Healthcare and medical systems.
- Home and Industrial automation using Bluetooth 5.
- Internet of Things wireless sensors for security applications.
Advantages of Bluetooth 5 Technology
Listed below are some of the advantages of Bluetooth’5 Technology that makes it an even more attractive prospect:
- Multiple devices can communicate with each other easily.
- There are hardly any compatibility issues while using it.
- Bluetooth 5 can be useful in various industries like Automotive, Home Automation, Consumer Electronics, Medical and Health, Mobile phones and Smartphones, Sports and Fitness, PC & peripherals etc. This technology also provides location based and retail services.
- Data transfer speed has increased 8 times in this technology. Much more data transfer is possible within a short time.
- It helps to reduce interference of other wireless technologies as Bluetooth devices coexist within the global IoT environment.
Disadvantages of Bluetooth 5 Technology
The disadvantages of Bluetooth’5 are:
- It slowly drains the battery of cell phone or other mobile devices. When Bluetooth is enabled, it continually scans for signals, looking for new devices to connect with, by using energy in the process.
- The Bluetooth security is weak compared to Wi-Fi and other wireless data standards.
Also Read: What is ZIGBEE Technology in IoT - Architecture, Network Topologies, Applications What is ZIGBEE Technology in IoT - Architecture, Network Topologies, Applications Virtual Reality (VR) Technology - How it Works, Components, Types & Applications