Hamming Codes are efficient error-correcting binary codes. They are used to detect errors that helps in recovering the original binary word. This post will discuss in detail about what are Hamming Codes, its working principle along with examples, Applications, Advantages and Disadvantages.
What are Hamming Codes
In digital communication system, the data transfer should be error free and with high accuracy. The data errors often results in the loss of important or secure data. To overcome this issue, a scientist named Richard W Hamming formulated an algorithm to detect and correct single-error correcting binary codes. His research paper was published in 1950 and later these codes were popularized as Hamming Code.
Fig. 1 – Richard W Hamming, Founder of Hamming Codes
The basic concept of Hamming Code is to add Parity bits to the data stream to verify that the data received is correct or matches with the input. These bits are transmitted in such a way that they identify where the error has occurred in the data stream and rectifies it.
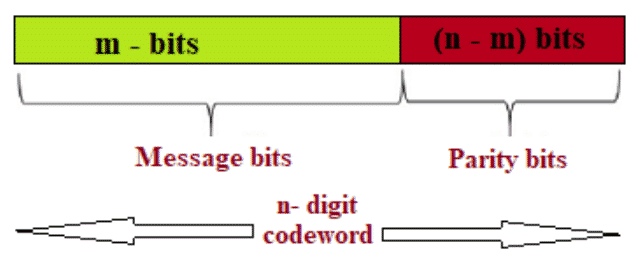
Structure of Hamming Code is shown in the Fig. 2. The entire data stream length comprises of Message bits (m) also called Data bits and Parity bits (n-m).
The final encrypted code word is [m+(n-m)].
Fig. 2 – Structure of Hamming Code
How does Hamming Code Work
The principle of error detection and correction of a code depends on its Hamming Distance. Let us examine two data strings: 10001001 and 10110001. In this example, bit positions 3, 4 and 5 are different. To calculate Hamming distance, Exclusive OR operation also called modulo addition is performed on the second data string and the number of 1’s in the result is counted.
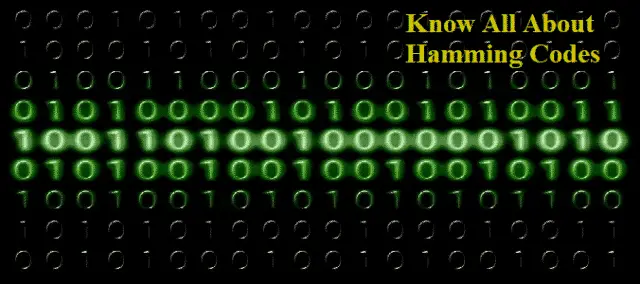
Fig. 3 – How Hamming Codes Work
In order to detect ’d’ errors, it needs a code with (d + 1) bits and similarly to correct d errors it needs a code with (2d + 1) bits
These Codes uses extra Parity bits to identify the error.
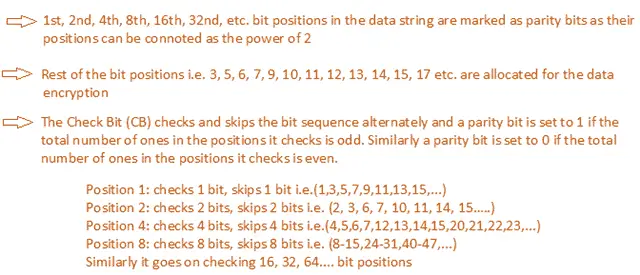
In order to calculate the code:
For Example:
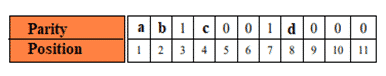
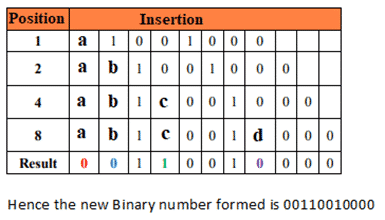
Let us consider the data 1001000
Thus we can interpret that, the check bits to be added is 4. These bits which are added to the original data is called Parity bits. Bit Length (7) + Parity Bits (4) = Encrypted Data (11 bits)
Applications of Hamming Code
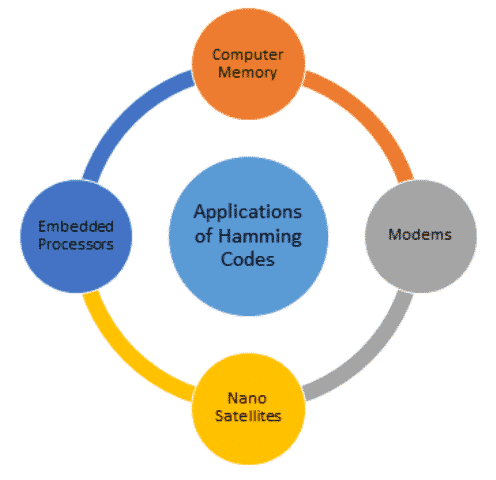
The applications of Hamming Code are:
- They are extensively used in telecommunication industry.
- They are used in computer memory, modems and embedded processors.
- They are used in Nano Satellites.
Fig. 4 – Applications of Hamming Code
Advantages of Hamming Code
The advantages of Hamming Code are:
- They are effectively used to detect and correct errors.
- Single-bit error correction using these Codes is effective on Data Stream Networks.
Disadvantages of Hamming Code
The disadvantages of Hamming Code are:
- Bandwidth usage is more.
- Extra parity bit added for error correction reduces the bit rate of transmitter.
Also Read:
Asynchronous Transmission - Communication Characteristics, Process of Data Flow, Advantages and Disadvantages
Barcode Number System - Types, Structure, How it works, Application, Advantage & Disadvantage
Robotic Process Automation (RPA) - Introduction, Works, Advantages and Applications